Search -
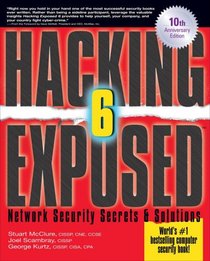
Hacking Exposed, Sixth Edition: Network Security SecretsAnd Solutions
Hacking Exposed Sixth Edition Network Security SecretsAnd Solutions
Author:
The worldAnd#39;s bestselling computer security book--fully expanded and updatedAndquot;For security to be successful in any company, you must Andlsquo;think evilAnd#39; and be attuned to your Andlsquo;real riskAnd#39;...Hacking Expose 6 defines both.Andquot; --Patrick Heim, CISO, Kaiser PermanenteAndquot;The definitive... more »
Author:
The worldAnd#39;s bestselling computer security book--fully expanded and updatedAndquot;For security to be successful in any company, you must Andlsquo;think evilAnd#39; and be attuned to your Andlsquo;real riskAnd#39;...Hacking Expose 6 defines both.Andquot; --Patrick Heim, CISO, Kaiser PermanenteAndquot;The definitive... more »
ISBN-13: 9780071613743
ISBN-10: 0071613749
Publication Date: 1/5/2009
Pages: 720
Edition: 6
Rating: ?
ISBN-10: 0071613749
Publication Date: 1/5/2009
Pages: 720
Edition: 6
Rating: ?
0 stars, based on 0 rating
Publisher: McGraw-Hill Osborne Media
Book Type: Paperback
Members Wishing: 0
Reviews: Amazon | Write a Review
Book Type: Paperback
Members Wishing: 0
Reviews: Amazon | Write a Review
Genres:
- Computers & Technology >> Certification >> CompTIA
- Computers & Technology >> Networking & Cloud Computing >> Networks, Protocols & APIs >> Network Security
- Computers & Technology >> Business Technology >> Hacking
- Computers & Technology >> Microsoft >> Networking
- Computers & Technology >> Security & Encryption >> Privacy & Online Safety
- Computers & Technology >> Security & Encryption